
Cloud Security: Challenges and Solutions
Security challenges when migrating to cloud and effective solutions.
Read MoreSharing knowledge and technology trends
Showing 25-36 of 100 posts

Security challenges when migrating to cloud and effective solutions.
Read More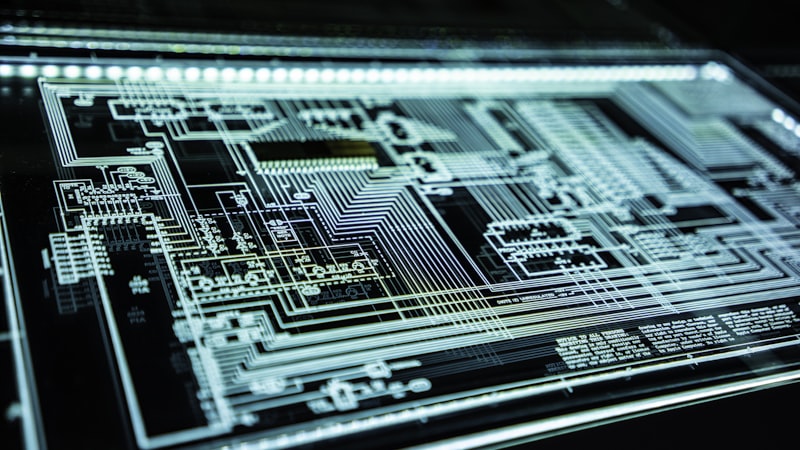
Pen testing helps discover vulnerabilities before attackers exploit them.
Read More
Strategies to protect businesses from increasingly sophisticated ransomware attacks.
Read More
API security techniques from authentication, rate limiting to encryption.
Read More
The Zero Trust model requires verifying every access regardless of network location.
Read More
Learn about the 10 most common web security vulnerabilities and how to prevent them.
Read More
Logs, metrics, and traces help detect and resolve incidents quickly.
Read More
Comparing two approaches to organizing source code and when to use monorepo.
Read More
Code review catches bugs early, shares knowledge, and improves software quality.
Read More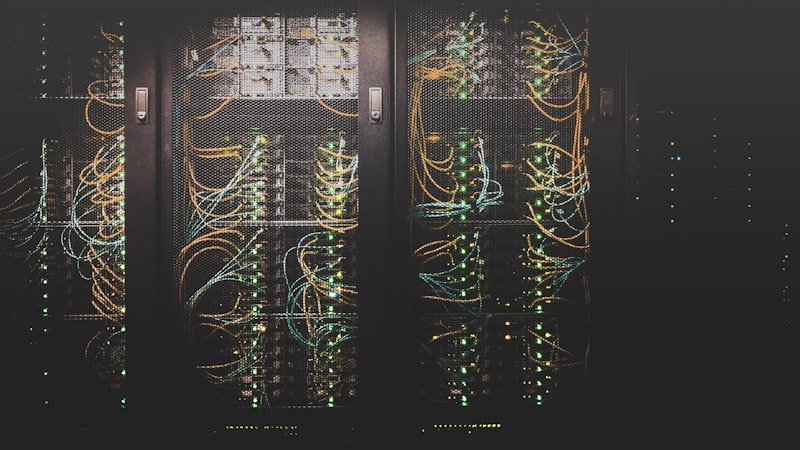
EDA enables loose coupling between microservices via message queues and event buses.
Read More
Principles for designing distributed systems handling millions of users.
Read More
Techniques for optimizing Core Web Vitals, lazy loading, and caching for faster websites.
Read More